Cybersecurity Management |
Protect and restore systems, assets, data, and capabilities, on-premise and in the cloud
Agilesys Cybersecurity solutions offering is a continuum from board level strategy to pragmatic implementation
|
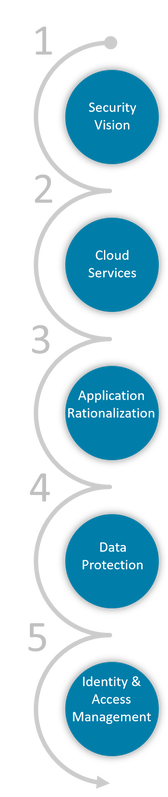
1) Strategize Including investment prioritization, risk modeling, capital / operating budgets, and resource planning linked to best practices across industry verticals 2) Transform
Policies, processes and tools, including current state assessment, roadmap, technical implementation, and governance models 3) Modernize
Security, architecture, and vendor risk for relevant applications, as well as capabilities assessments to industry frameworks such as NIST and CSA 4) Defend
Establish compliance, encryption, and roles-based controls, enabling on-premise and multiple cloud-based data networks 5) Safeguard
Manage privileged and non-privileged access using risk-based and adaptive multi-factor authentication |